
Samuel White
Total 194 Posts
This cybersecurity and cryptocurrency guru believes that life without the Internet can only exist on Mars. He picked Amsterdam as his hiding place to explore the worldwide cobwebs.
Brazil Bans Social Media Platform X Amid Legal Dispute with Elon Musk
Supreme Court Justice Alexandre de Moraes, the judge presiding over the case, has also imposed a daily fine of $9,000 for users attempting to bypass the ban via VPNs.
Apple Complies with Chinese Order to Remove WhatsApp and Threads from App Store
Apple stated that it is obligated to comply with the laws of the countries where it operates, indicating a complex balance between adhering to local regulations and navigating the broader implications for global tech operations.
Google Commits to Destroying Illegally Collected Incognito Browsing Data
Under the terms of the proposed settlement, which still requires approval from a California federal judge, Google will destroy or de-identify billions of records of web browsing data collected under the guise of private browsing.
Apple Bolsters iMessage Security Against Future Quantum Threats
By constantly refreshing encryption keys and integrating post-quantum cryptography with existing protocols, Apple ensures that iMessage remains at the forefront of secure messaging.
Google Introduces Passwordless Sign-In with Passkeys as a Default Option
Google has been actively promoting passkeys, which align with the industry's goal to reduce reliance on passwords. The company encourages users to adopt passkeys as their primary sign-in method, emphasizing their ease of use and enhanced security.
PayPal Launches Its Own Dollar-Backed Stablecoin PYUSD
While initially rolling out to eligible U.S. PayPal customers, this stablecoin is poised to play a pivotal role in bridging the gap between traditional fiat currencies and the rapidly evolving realm of digital assets.
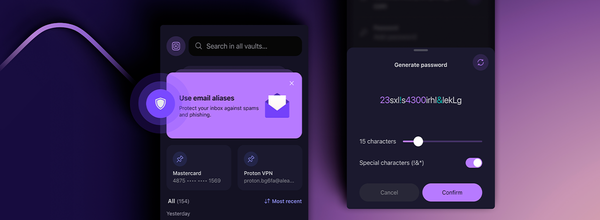
Proton Pass End-to-End Encrypted Password Manager Is Available to Everyone
The password manager generates unique and complex passwords for users, making it easier to maintain strong security practices. With seamless synchronization across devices, users can access their login credentials whenever and wherever they need them.